I’m playing around with an Azure Function that I’m going to eventually call from an Azure Automation runbook (post to come in the near future).
During this process, I learned some pretty key things as I was testing and going along. I’m a little embarrassed to post them publicly, but eventually a non-coder like myself somewhere is going to be trying the same thing and maybe this will help.
Function error-ing out during testing
In my function, I used a ForEach loop to add a string to a List<string> for each instances of a collection. My function would compile just fine but would always error out on this one line, with a really generic error. I only knew it was erroring out on this line because I placed a log output on the next line and it would never reach it.
[Error] Executed 'Functions.HttpTriggerCSharp2'
This was my poor coding skills, not beginning the list properly. I was starting it like this:
List<string> collectedIP = null;
List<string> collectedIP = new List<string>();
Building the query string
I want to pass in a parameter to my function, using the query string. At the same time, I also want to use a function key so that this can’t be run anonymously.
Originally, I was trying this, with the ampersand delineating the second query parameter (after the function key):
Invoke-WebRequest https://appname.azurewebsites.net/api/functionName?code=functionKey&name=www.microsoft.com |
In PowerShell, this returned the error:
The ampersand (&) character is not allowed. The & operator is reserved for future use; wrap an ampersand in double quotation marks ("&") to pass it as part of a string. |
So I tried this string:
Invoke-WebRequest 'https://appname.azurewebsites.net/api/functionName?code=functionKey"&"name=www.microsoft.com' |
But then I received the error:
Invoke-WebRequest : The remote server returned an error: (401) Unauthorized. |
Well, I knew it wasn’t unauthorized because it ran properly in the browser. The actual fix was stupidly easy, I hadn’t put any quotes around the whole string – either single or double quotes was fine:
Invoke-WebRequest "https://appname.azurewebsites.net/api/functionName?code=functionKey&name=www.microsoft.com" |
TLS Support in PowerShell
When I got to actually testing my function, I tried to call it from PowerShell in this format:
Invoke-WebRequest 'https://appname.azurewebsites.net/api/functionName?code=functionKey' |
However, upon doing so I received this error:
iwr : The underlying connection was closed: An unexpected error occurred on a send. |
A google search led me to discover that PowerShell by default will attempt to use TLS 1.0 for Invoke-WebRequest, unless you’re using PowerShell Core 6.
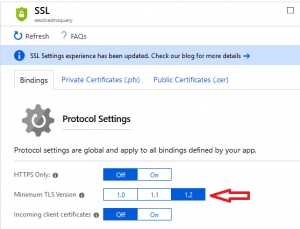
My Azure Function uses TLS 1.2 by default and as a minimum. This can be found on the “Platform Settings” page of the Function, under “SSL”:
The solution (at least as a workaround) is to force that session to use TLS 1.2 like this:
[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12 |
Primary source for this information was here.