My Commvault disk library is nearing 90% capacity, which is a growing cause for concern. The disk library is provided by a Dell MD1400 with 12x6TB SAS drives, which was originally configured as a 10 disk RAID6 set with 2 hot spares (~45TB usable) on the PERC H830 card.
As an intermediate step before purchasing an additional disk shelf, I did the following to give a little breathing room.
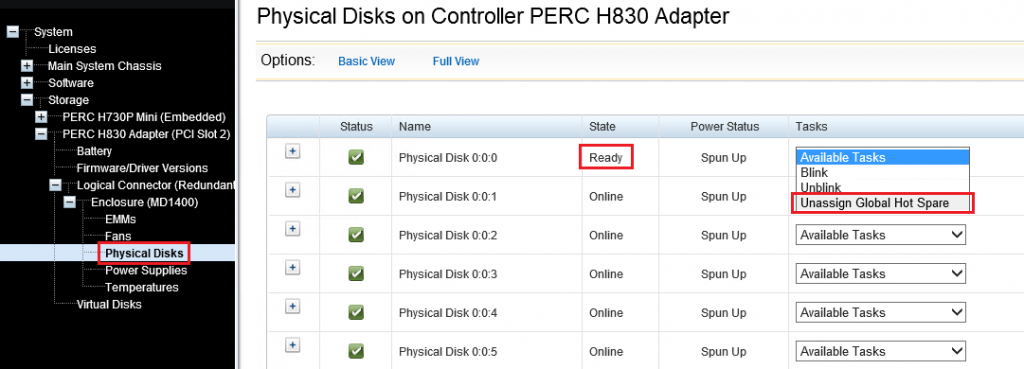
- Using the Dell Open Manage Server Administrator (OMSA), I located one of the hot spare drives and unassigned it.
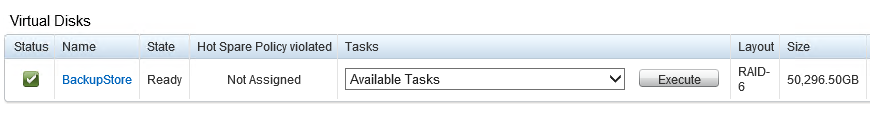
- Still within OMSA, I chose the “Reconfigure” option on my Virtual Disk, keeping the RAID level at 6 but adding in the new available capacity.
- Then I waited. It took 16 days for the reconfiguration to complete as the RAID6 parity was re-spread/calculated across the set. This left me with a ~50TB virtual disk.
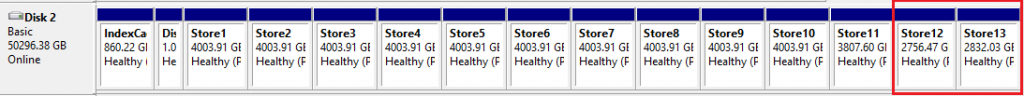
- Within Disk Management, I carved the free space into two additional ~3TB volumes, which are mounted within a standard disk library path of L:\DiskLibrary. This size adheres to the recommendations given to us by our professional services partner.
- During the original configuration, we used Automated Mount Path Detection, to point to L:\DiskLibrary:
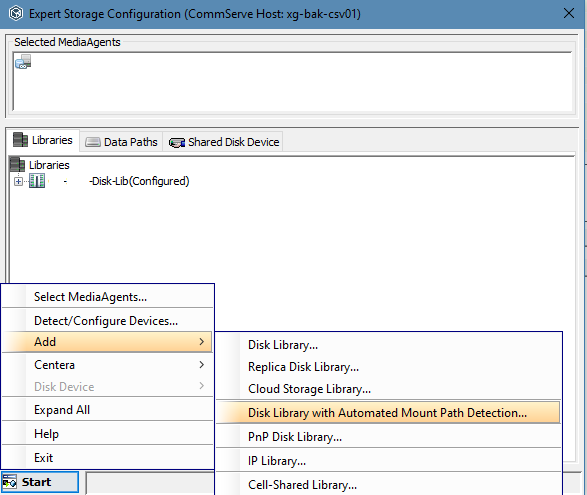
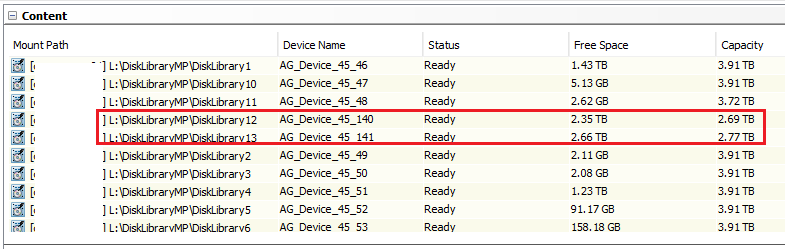
- Due to this, the new mount paths were picked up automatically after about 15 minutes, and appeared within the list of mount paths under the library:
Checking the Disk Usage tab on the properties of the library dropped utilization down to 80%, and provided us some time to address the growing data concerns.
